Smartphone penetration and mobile internet connectivity are rapidly growing in emerging markets, empowering consumers and granting them access to knowledge. Across multiple countries and on a large scale, it seems that low-cost Android smartphones are being sold with pre-installed malicious software designed to commit digital advertising fraud. For the unsuspecting users of these smartphones, it results in:
- Systematic collection & transfer of personal information to a 3rd country server
- Depletion of their mobile data allowance
- Ad fraud, which results in fraudulent transactions and charges to their pre-paid airtime
Let’s take a step back first
Carrier billing, a payment method allowing mobile users to purchase digital services by charging payments to their airtime balance, is the only way mobile users can pay for digital services in emerging markets. It is now easier than ever for an emerging market consumer to complete an online transaction with just a simple, one-click payment, thanks to an advanced technology used by mobile operators. No need to fill up long forms with any kind of payment or personal details.
Online ad fraud, in general, is mostly about fake impressions and clicks, with fraudsters, who are incentivized by the payouts offered for driving sales through digital advertising, using software to artificially generate impressions and clicks. This impacts the advertisers by inflating the actual cost of advertising. In emerging markets, it also impacts the end consumer, as fraudulent online clicks can trigger unwanted purchases and consequently charges to their airtime credit, but also deplete their steeply priced data allowance.
There are significant differences in emerging markets that connect the dots:
- Most people are unbanked and prepaid mobile subscribers, using their airtime to pay for digital services
- The cost of data is relatively higher, compared to developed markets. In Africa, for example, 1GB for prepaid subscribers costs the equivalent of 16h of work on minimum wage.
Unveiling the investigation
Starting in November 2017, Upstream’s carrier-grade platform Secure-D, protecting MNOs and their subscribers against online transaction fraud, detected a high concentration of blocked transaction attempts in Brazil coming from Android smartphones sold under the brand name Multilaser. Almost at the same time, a similar pattern was observed in Myanmar from Android smartphones branded as Smart.
While it is common for fraud attempts to be coming from a specific application or IP address, this was the first time fraud was seen being concentrated in specific devices, and in 2 different countries.
During that period, 45% of all fraudulent transaction attempts for a premium digital service (an online games portal) in Brazil originated from Multilaser devices (while Multilaser’s market share is not as high). And 99% of all transaction requests from Multilaser branded phones in Brazil were blocked as fraudulent by Secure-D’s fraud detection algorithm.
At the same time, in Myanmar, 8% of all fraudulent transaction attempts for the same premium digital service were originated from Smart devices (by far the highest rate to be coming from just one brand). And 98.5% of all transaction requests from Smart branded phones in Myanmar were again flagged as fraudulent.
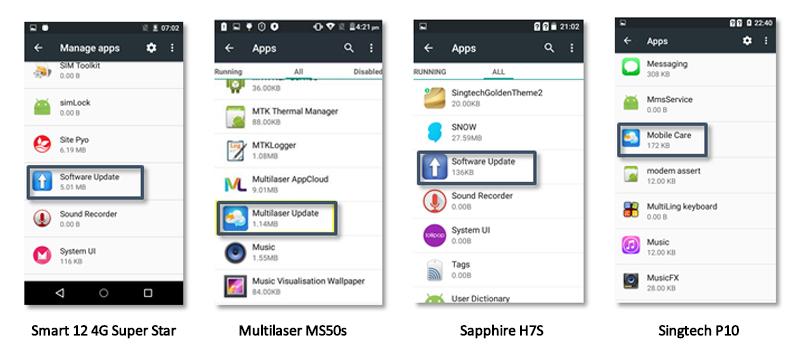
What caught our attention was that the same application, named com.rock.gota, was sending these fraudulent transaction requests in both Brazil & Myanmar. com.rock.gota is an application that cannot be found on Google Play store; and on their phones, users usually see it under the name ‘Software Update’ or ‘Mobile Care’.
com.rock.gota behaviour analysis
Upstream’s security analyst team purchased a set of devices with a high volume of fraudulent attempts in both Brazil and Myanmar from physical electronics stores in those markets. In all such devices, com.rock.gota was pre-installedand was identified as soon as the phones were turned on for the very first time.
At first, a Multilaser MS50S device was investigated and placed in a “sandbox” environment in which all network traffic (data transmitted from and to the device) was recorded.
Upon first powering-on, the device initiated numerous encrypted data transmissions to and from a server located at the URL http://api.rock.fotapro.com/, which points to an unsecure server located in Singapore and operated by Gmobi.
Gmobi, according to its website, is a “Performance-Based Ad Platform that Enables Content Monetization and Global Users Acquisition” with a reach of “150M installs base in more than 120 countries” and is headquartered in Shanghai, China (www.generalmobi.com), claiming to “serve customers in China, Taiwan, South East Asia, the US, India, Russia”.
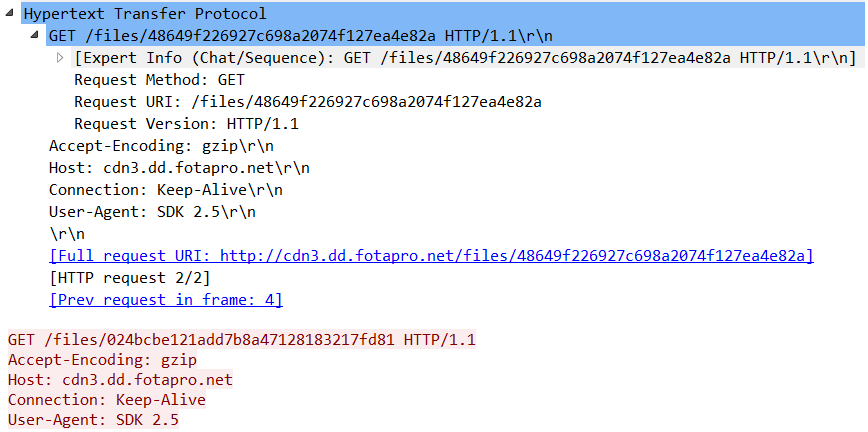
While keeping the Multilaser device under monitoring and without having accepted the terms & conditions of com.rock.gota, nor having interacted with the app, the network traces were analyzed to identify multiple requests to download advertising material (web banners) in the background, without making them visible to the user. One such case requested and downloaded the contents of the url: http://cdn3.dd.fotapro.net/files/48649f226927c698a2074f127ea4e82a (still active at the time of writing).
Which points to the below creative of an Uber promotional campaign, although whether or not this is an official and approved Uber campaign is unclear.

The pre-installed application com.rock.gota that was identified by Secure-D as attempting to fraudulently purchase services on behalf of users, has been previously documented by antivirus company Dr. Web and other sources, as collecting information from the device, including email, GPS location (i.e. exact street & number, city, state, country), device’s unique identifiers, data that can be used to personally and uniquely identify the owner of the device.
It is important to note that this application cannot be uninstalled by users, unless they perform a complex rooting procedure which may even result in their warranty being voided.
Identical findings were witnessed by Secure-D analysts in follow-up investigations on the Singtech P10, Smart 12 4G Super Star and Sapphire H7S devices purchased in Myanmar.
Besides being a Performance-Based Ad Platform, Gmobi provides a Firmware-Over-The-Air technology (FOTA) to mobile device manufacturers as an alternative to Google’s official offer, to allow them to update the device’s firmware over the internet. Google requires manufacturers to go through a certification process before allowing them to use the official method for firmware updates.
It seems that certain manufacturers opt to go with Gmobi’s solution for firmware updates. This does not in itself suggest that manufacturers install such software with the intention of defrauding their customers. It does, however, point to manufacturers needing to better control software pre-installed on the devices they sell.
Consequences and effects on users
It seems that users across multiple countries are being affected by the pre-installed application com.rock.gota, and at large scale, resulting in:
- Systematic collection & transfer of their personal information to a 3rd country server without their consent.
- Depletion of their data allowance -a huge issue in emerging markets where the cost of data is dramatically high. In Brazil, for example, 1GB for prepaid subscribers costs the equivalent of 6h of work on minimum wage.
- Fraudulent transactions and charges to their prepaid airtime, the only way users can pay for digital services in emerging markets, as most people are unbanked. In Africa, 94% of the population has no account with a financial institution.
Affected markets
According to Secure-D findings, users in over 8 emerging markets are affected by this particular malware. The ones most affected over the last two months are in Brazil, Myanmar and Malaysia.
In Brazil, Secure-D detected over 2 million fraudulent transaction attempts coming from Multilaser devices over one single month (November 2017), and for multiple digital services. These attempts represented 41% of the total 247,484 unique phone numbers that fraudulently attempted to purchase one of the services.
At the same time, in Myanmar, Secure-D spotted over 114,000 fraudulent transaction attempts coming from Smart branded devices. Those 114,000 fraudulent attempts represented 21% of the total 110,306 unique phone numbers that fraudulently attempted to purchase a digital service.
Conclusion
As the devices come with the malware pre-installed, consumers are left helpless in protecting themselves from the adverse effects of com.rock.gota. Uninstalling it involves attaining root access to the Android operating system, a highly complex procedure even for savvy users. This is not a practical solution as very few people can perform it, let alone the average user in Brazil or Myanmar.
Overall, malware fraud (not Gmobi specific) observed during the month of June 2018, across 8 emerging markets and 12 carriers, Secure-D has prevented fraudulent subscriptions to digital services that would have resulted in 20m USD being billed to consumers’ airtime/credits. And this figure does not include the additional value of the related data allowance depletion that was inflicted on unknowing mobile users.
Secure-D combines machine learning algorithms with payment processing workflows to protect mobile operators and their subscribers against online transaction fraud and data depletion, caused by all types of malware and other online threats. The platform processes over 100 million transaction requests per month, has detected and blocked over 42,000 malicious apps and has identified more than 2.7 million infected smartphones.
—
Upstream has worked with The Wall Street Journal to bring this story to light. You can read their write up here.

